What is phishing?
Phishing is a common type of cyberattack. It targets individuals through the means of email, text messages, phone calls, and other forms of communication. A phishing attack aims to trick the recipient into falling for the attacker’s desired action, which could include revealing sensitive information (I.e. name, social security number, etc.), system login credentials, or opening a malicious attachment or visiting a malicious site.
At CU Boulder, OIT works with students, faculty and staff to identify, report, and prevent phishing attempts on the CU Boulder email system.
Spot phishing scams
Identify phishing by remembering to SLAM:
- Sender: Look for misspelled email addresses or masked sending addresses that don’t match the expected sender’s name or address. If you don’t recognize the sender, don’t proceed.
- Links: Use your mouse to hover over (but don’t click on) links to check them out before you click – especially links you don’t recognize. Instead, directly type the website URL into your browser.
- Attachments: Do not open unexpected attachments – even from people you know. Sometimes people you know have had their account compromised or don’t realize they’re forwarding a phishing attack.
- Message: Check emails, including subject lines, for suspicious language, misspelled words and bad grammar – hallmarks of a mass-produced phishing scam.
Always remember that legitimate companies and organizations will never email or text you to ask for passwords, social security numbers, money, or other sensitive information.
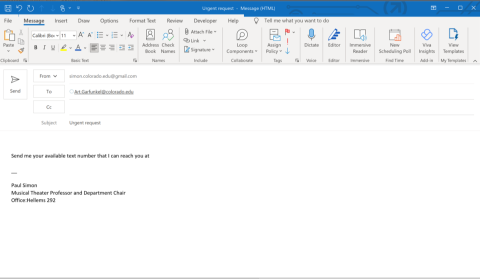
Phishing email examples
Click the photos to enlarge
How to report a phishing scam
Preferred method: Report via Microsoft Outlook
- In your mailbox, right click on the email.
- From the pop-up menu, select Report phishing.

- If you do not see Report phishing as a listed option, you can also click the Report button on the upper mailbox banner then click Report phishing.

Alternative method: Send the phishing message as an attachment
Follow the below methods to send suspicious messages as an attachment (RFC-822 MIME encoded) to phish@colorado.edu.
Apple Mail
- Click on the email you want to forward
- Select File Save As, Format - Raw Message Source
- Create a new message
- Attach raw source file(s) to the new message
- Send to phish@colorado.edu with "PHISHING" in the subject line. Click Send.
Gmail
- Open the message you want to forward.
- Click the Forward link in the box below the message.
- Add the new recipient(s) and any additional text to your message.
- Send to phish@colorado.edu with "PHISHING" in the subject line. Click Send.
Office 365 Outlook on the web
- In the upper left-hand corner click on the + icon then select New message
- Drag the suspicious email into the body of the new message. This will add the suspicious email as an attachment.
- Send to phish@colorado.edu with "PHISHING" in the subject line. Click Send.
Mozilla Thunderbird
- Click on the email you want to forward.
- Select Message, then Forward As, and then select Attachment.
- Send to phish@colorado.edu with "PHISHING" in the subject line. Click Send.